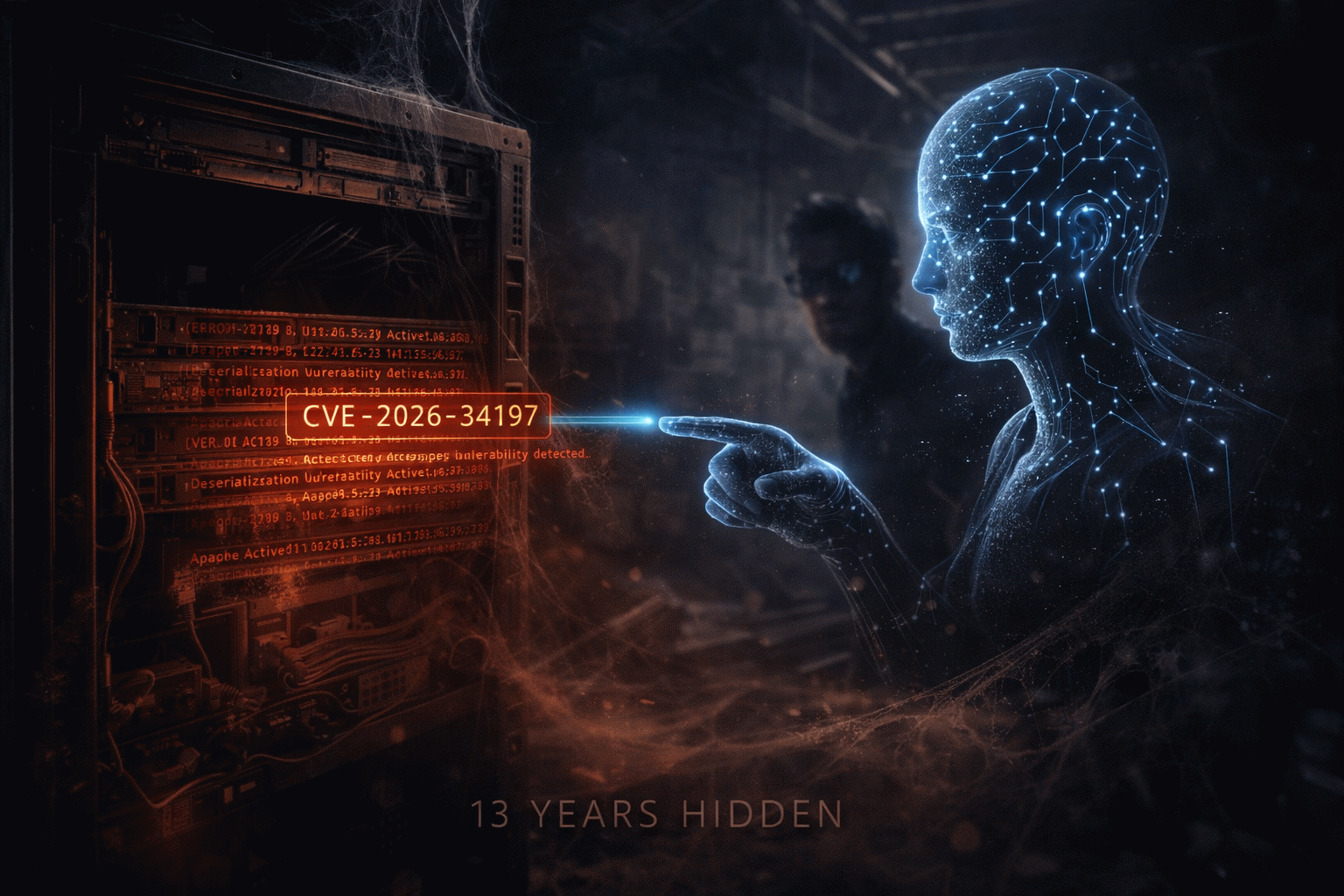
On April 16, 2026, CISA added CVE-2026-34197 to its Known Exploited Vulnerabilities catalog, forcing US Federal Civilian agencies to patch by April 30. On the surface, it is another RCE: CVSS 8.8, unauthenticated code execution, impacts Apache ActiveMQ Classic before 5.19.4 and 6.x before 6.2.3. The interesting part is not the CVE — it is the backstory.
A Bug That Waited 13 Years
Naveen Sunkavally, a researcher at Horizon3.ai, disclosed the flaw publicly on April 9. According to his write-up, the core vulnerability has existed inside ActiveMQ for roughly 13 years. The exploit path runs through Jolokia — an HTTP-to-JMX bridge that exposes broker management operations as a REST API. By crafting a specific request, an attacker can force the broker to fetch and process a remote Spring XML configuration file. Spring XML, as most enterprise developers know the hard way, is essentially a code-execution primitive. So: unauthenticated REST request → forced XML retrieval → arbitrary code on the broker. Thirteen years. Fortinet FortiGuard observed dozens of exploitation attempts in the days following disclosure, peaking on April 14.
Two Morals, One CVE
Every significant CVE has a moral. This one has two.
The first is classic: old, widely-deployed enterprise middleware is a graveyard of assumptions that were "probably fine in 2013." Jolokia-enabled management endpoints, default listen addresses, legacy XML parsers — each one individually defensible, together a primitive for remote code execution. ActiveMQ is running inside banks, insurance backends, and critical infrastructure today. Nobody was asking this specific question about this specific combination until now.
The second is new, and more culturally interesting. Naveen's public disclosure explicitly credits Claude — Anthropic's AI assistant — as a collaborator in the audit. Not a tool that produced the finding, but a partner with which the researcher iterated through ActiveMQ's behavior, weighed hypotheses, and walked down the chain of call sites that ultimately connected an HTTP endpoint to Spring XML execution. This is not "AI found the bug." It is "a skilled researcher, working with an AI that can hold a large codebase in context, found a bug that had been invisible for 13 years."
My Take: AI Changes the Tempo of Security
For most of 2024 and 2025, the industry debate was: will AI change offensive security more, or defensive security more? The honest answer, which this case embodies, is that AI changes the tempo of both — and tempo is the decisive variable in security.
On offense, a single researcher with an AI collaborator can now do, in weeks, audit work that used to require a specialized team and months of domain context. CVE-2026-34197 is not the last 13-year-old bug that AI co-piloting will surface. Expect a lot more. Every widely-deployed open-source middleware is about to get re-audited with capabilities nobody had in 2013.
On defense, the operational implication is brutal. Organizations that still believe "we are safe because this component has had no high-impact CVE in a decade" are running on a stale threat model. "No CVE in a decade" used to be a sign of maturity. In 2026, it is just as likely to be a sign that nobody had the compute time to look hard enough. If you run ActiveMQ, or any long-lived message broker, the correct posture is: patch immediately (5.19.4 / 6.2.3), disable Jolokia if you do not need it, constrain egress from broker hosts so they cannot pull remote XML, and commission an AI-assisted audit of your own.
The poetic bit: an AI helped find a vulnerability created long before that AI existed. That compression of time — a human plus a model, together recovering context that drifted away over thirteen years — is the actual story. And it is going to keep happening.