In 13 days, a single researcher did what most nation-state actors spend years trying to do: turned Microsoft's own flagship security product into an attack surface.
In early April 2026, someone operating under the handle "Chaotic Eclipse" — also referenced as "Nightmare Eclipse" — began dropping proof-of-concept exploits on GitHub for three separate Windows Defender zero-day vulnerabilities. Each release came with a blog post, a public justification, and an explicit claim that Microsoft's vulnerability reporting process had failed them. The result is one of the most consequential security stories of 2026, and one that should genuinely worry anyone running Windows in production.
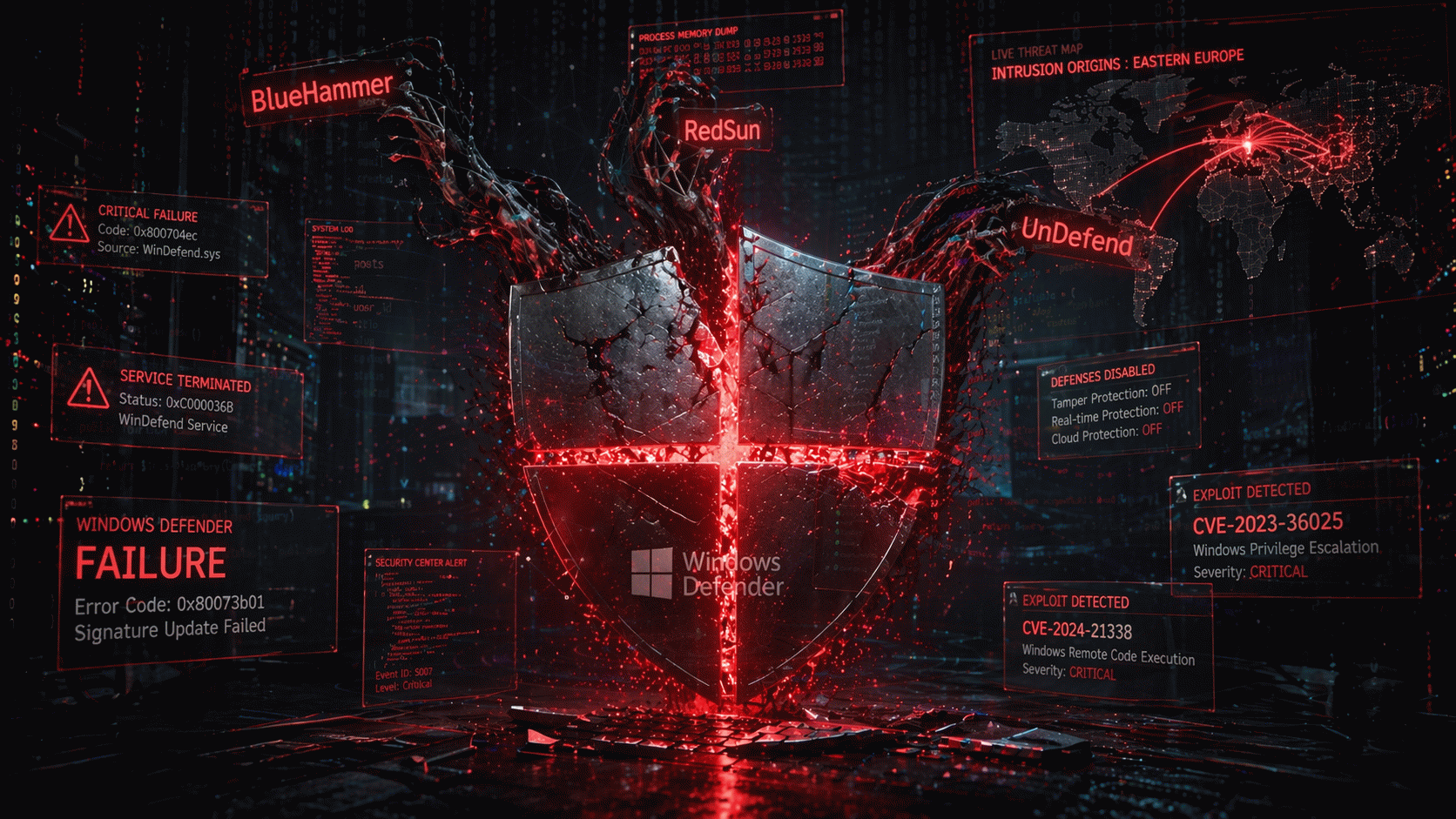
The Three Exploits
BlueHammer (CVE-2026-33825) abuses Defender's file remediation logic. When Defender detects a malicious file and starts to quarantine it, BlueHammer uses a batch opportunistic lock to pause Defender mid-operation, then swaps an NTFS junction point in place that redirects Defender's target path to C:\Windows\System32. When Defender resumes — running as SYSTEM — it obediently writes to the redirected location. A standard-user action becomes a SYSTEM-level write. Microsoft patched this one as part of the April 2026 Patch Tuesday.
RedSun attacks a different surface. It abuses Defender's handling of cloud-tagged files to overwrite system paths. Critically, RedSun still works on fully patched Windows 10, Windows 11, and Windows Server 2019 and later systems, even after the April patches.
UnDefend is the one keeping threat hunters up at night. It does not escalate privileges — it silently cripples Defender itself. A standard user with no admin rights can block Defender from receiving signature updates, or under certain conditions disable it entirely. An attacker who pairs UnDefend with any commodity malware effectively turns off the victim's front-door alarm before walking through it.
Huntress Labs has confirmed all three exploits are being used in live attacks. BlueHammer has been seen in the wild since at least April 10, 2026. One confirmed intrusion was traced back to a Russian IP accessing the compromised environment through a FortiGate SSL VPN.
Why This Zero-Day Story Matters More Than Most
Zero-day disclosures happen every month. This one is different for three reasons.
First, the attack surface is Defender itself. Defender runs on hundreds of millions of Windows endpoints by default. It is the single most widely deployed piece of security software on the planet. Every one of these exploits turns a defensive asset into an offensive one.
Second, the disclosure pattern was deliberate. Chaotic Eclipse did not privately report and wait for a patch. They dropped the exploits with full documentation, publicly, as a form of protest. That model — weaponized disclosure — will encourage imitators and makes Microsoft's patching cadence an operational problem for every IT team on earth.
Third, two of the three remain unpatched as of mid-April. There is no clean mitigation path for RedSun and UnDefend yet. Organizations running Defender have a choice between living with active exploitation or deploying third-party EDR as a compensating control — exactly the outcome Microsoft has spent a decade trying to avoid.
My Take
The uncomfortable lesson here is not specifically about Defender. It is about the fundamental trust model of bundled security tools.
For twenty years the industry has converged on a single pattern: ship powerful, privileged, deeply integrated security agents to every endpoint. Defender, CrowdStrike, SentinelOne — all of them live at ring 0 or close to it. When they work, they are invaluable. When they have a vulnerability, they are a catastrophe, because the very privileges that make them effective defenders make them devastating when subverted.
The Chaotic Eclipse disclosures do not prove Defender is uniquely insecure. They prove that any security agent with SYSTEM-level privileges is one bug away from becoming the most dangerous program on the machine. The industry response cannot be "patch faster." It has to be architectural: reduce the privilege surface, sandbox the remediation logic, and treat the security agent itself as an attack target from day one.
Until that happens, every organization running Defender — which is most of them — needs to accept a plain fact: right now, the antivirus is a way in.