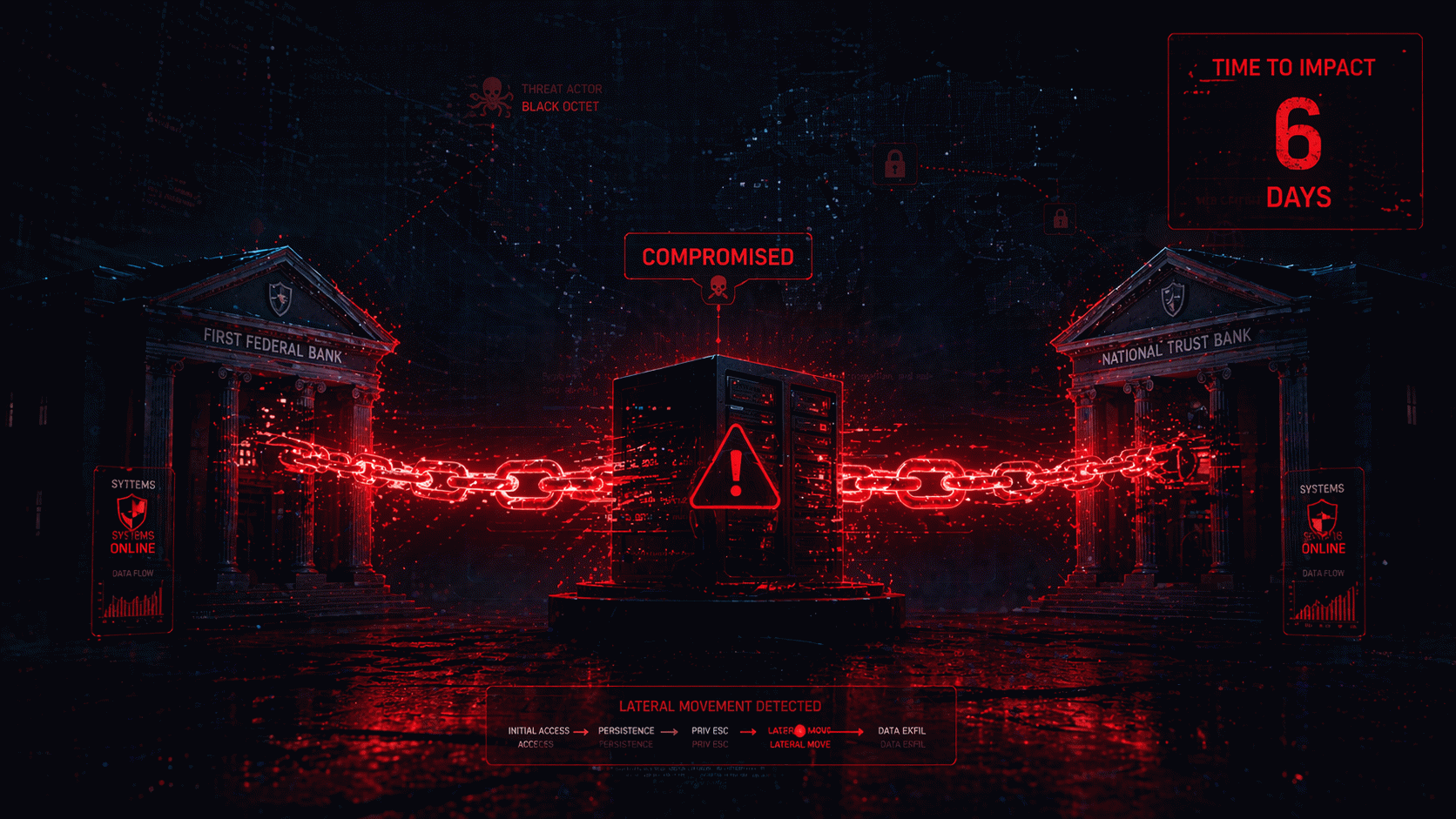
Yesterday — April 23, 2026 — two well-known U.S. banks quietly confirmed something that is rapidly becoming the single most common pattern in modern cybersecurity incidents: they had been breached through a shared third-party vendor. Citizens Bank and Frost Bank both appeared on the dark-web leak site of the Everest ransomware gang, which gave the institutions a six-day countdown before threatening to release the stolen data.
Citizens Bank stated publicly that the incident involved data extracted from a third-party vendor, with most of it being masked test data and a limited set of customer information impacted. The bank emphasized there was no evidence of unauthorized access to its own internal network. Frost Bank, for its part, confirmed its vendor had been compromised and that customer data may be at risk; it has engaged external cybersecurity experts to investigate.
On paper, these are textbook breach disclosures. In practice, they illustrate a problem that has been festering in financial services for years — and that 2026 is forcing everyone to finally confront.
The third-party problem is now the security problem
Banks spend hundreds of millions of dollars annually hardening their own perimeters. Zero trust, continuous authentication, 24x7 SOCs, regulatory audits every quarter. None of that matters if the fintech vendor they outsource card servicing to, or the document management platform their marketing team uses, or the call-center analytics tool someone approved in 2019, gets popped.
The Everest gang understands this better than almost anyone. Rather than hitting a hardened bank directly, they go after a shared supplier, grab data from dozens of downstream clients, and post them all on their leak site at once. From the attacker's point of view, one successful breach yields many ransoms. From the bank's point of view, a supplier you've never directly interacted with suddenly has the power to end your quarter.
This isn't new. What's new is the frequency. In the first four months of 2026 alone, third-party breaches have accounted for more than half of confirmed financial-sector incidents tracked by breach trackers. Booking.com's massive breach earlier this month followed the same pattern. So did the attack on Basic-Fit, Europe's largest gym chain, which exposed data on over a million members.
What's actually at stake for customers
The specifics of what was stolen in the Citizens and Frost incidents are still unfolding, but based on the breach class, customers should expect at minimum: names, email addresses, phone numbers, partial account identifiers, and possibly transaction metadata. The banks insist that core banking credentials were not compromised, but even partial data is more than enough to fuel targeted phishing, SIM-swap attempts, and account-takeover social engineering.
If you bank with Citizens or Frost, the right moves today are straightforward. Enable multi-factor authentication on every banking surface, and not SMS-based if you can avoid it. Assume you will receive a convincing phishing call or text within the next 30 days claiming to be from your bank's fraud department. Treat any incoming "security alert" with extreme skepticism, and call the bank using the number on the back of your card — never the number in the message.
What every other business should learn from this
Even if your company has nothing to do with banking, the Citizens-Frost-Everest story contains three lessons you cannot ignore.
First, you do not know your vendor's vendors. Almost every major breach in 2026 involves a fourth or fifth party — a sub-contractor of a vendor of your vendor. Mapping that chain is painful, boring, and unavoidable. If you have not done a vendor-chain review this year, you are overdue.
Second, static vendor security questionnaires are no longer sufficient. Attackers move weekly. A SOC 2 report from nine months ago tells you almost nothing about whether your vendor is currently compromised. Continuous monitoring, live threat-intel feeds, and real-time dark-web surveillance for your supplier portfolio are now baseline — not advanced.
Third, rehearse the response. The banks on Everest's leak site had six days. Most organizations, if they were named today, would burn three of those days arguing about who owns the incident, another two on legal review, and discover on day six that their public-facing comms weren't pre-approved. Run a tabletop exercise on a third-party breach this quarter. Run another one next quarter. Make the decisions before the clock starts.
My take: the perimeter has left the building
For twenty years we've talked about "the disappearing perimeter." April 2026 is when that phrase stops being architecture jargon and becomes the literal operating reality of every CISO. There is no perimeter. There is your network, there are your partners' networks, there are your partners' partners' networks, and attackers will find the softest one. The only durable defense is to assume breach at every boundary — including boundaries you didn't know you had.
Citizens and Frost will, in all likelihood, weather this incident. They have the balance sheets and the legal teams to absorb the hit. The real victims will be their customers, and the real lesson is for the rest of us: if two household-name banks can be brought to the brink of a public data dump by a vendor most of their customers have never heard of, so can you. The six-day countdown is just a clock. The vulnerability is the supply chain.